Security is a must for today’s mission applications
Software is developed using a set of practices known as DevOps (Development and Operations). The processes are automated so teams can build, test, and release software rapidly. DevSecOps bolsters this philosophy by making security an integral part of the development and operations process. Security for each stage of the software development lifecycle is integrated and automated, mainly through infrastructure and configuration.
With DevSecOps, organizations can achieve the agility, speed, quality, and security required in today’s dynamic IT landscape.
Complying with CMMC
The Department of Defense’s (DoD) Cybersecurity Maturity Model Certification (CMMC) reinforces the need for increased cybersecurity at all levels within an organization. This need is why our approach to DevSecOps ensures that: 1) security is a part of infrastructure and configuration management, 2) regular security assessments are conducted, and 3) system and information integrity are inspected throughout the software development process.
Our DevSecOps process reviews code, checks open-source library security, and eliminates bad coding practices early on. These processes, combined with automated testing and delivering the code iteratively in smaller increments, bring cybersecurity agility with security audits that can be performed quickly and effectively.
Security integrated with all pipelines
Automated and integrated operations bring speed to solutions. In our experience, we have observed siloed processes (among developers, engineers, and data scientists) that result in slow missions with too many tools, too many manual processes, and worse, lack of communication. All of these equal mounting technical debt.
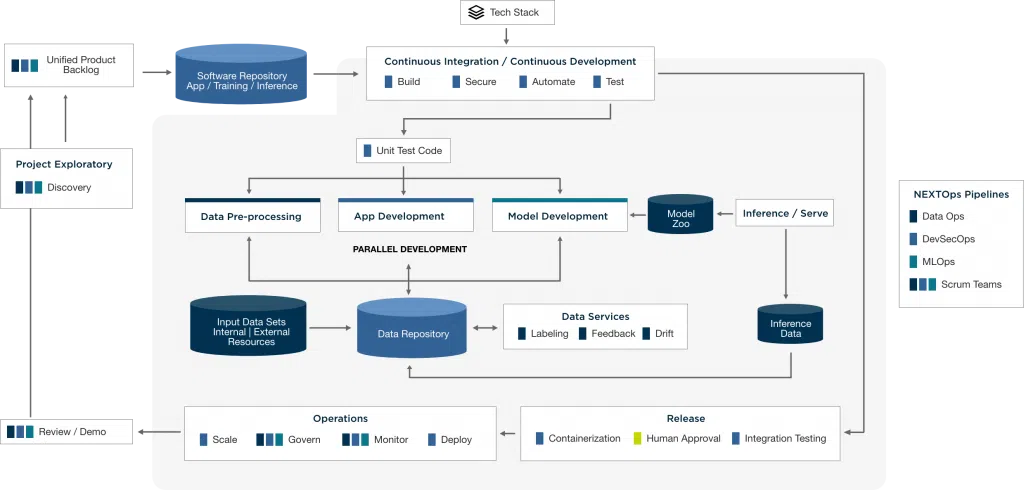
NT Concepts built our NEXTOps Framework to integrate development, data operations, and machine learning operations for collaboration, automation, scalability, and security. DevSecOps manages the complete ecosystem, baking in security to the operations, and facilitating the continuous development and delivery of agile solutions.
Within this framework, DevSecOps integrates with the:
- DataOps (Data Operations) pipeline to create an automated and continuous trusted data flow for DevSecOps and MLOps ingestion and use. This benefits most organizations because data is often unlabeled, stored in disparate formats, and not optimally transformed for rapid ingestion into analytic pipelines. DataOps iteratively enhances data quality, literacy, and governance.
- MLOps (Machine Learning Operations) pipeline to leverage DevSecOps and DataOps processes at every step, consuming the data pre-processing, model training, and serving pipelines. Machine learning isn’t a stand-alone data science exercise. Data, systems, and operations are inextricably linked to machine learning algorithms to ensure models are trained and validated appropriately. With MLOps, model development is iteratively run, and output continuously flows through the DevSecOps process for consistent deployments and maintenance.
Modularity is key
NT Concepts’ DevSecOps is modular in nature: new tools can be swapped in at any time as others are sunset. We designed the process this way to allow flexibility in our client environments. Organizations may already have chosen tools for the DevSecOps process (e.g., Jenkins, Fortify, or Chef)—and/or they may want to incorporate new, innovative tools. (see Figure 1 in which the blue boxes represent the modules in which various tools can be used). To maintain compliance with DoD’s DevSecOps Reference Design, we use industry-leading tools (e.g., Jenkins, SonarQube, and TerraForm) for their best-of-breed reputations and long histories in their respective categories.Our combination of people, processes, and tools enables operational efficiency
At NT Concepts, we continually add certified Amazon Web Services (AWS), Google Cloud Platform (GCP), and Microsoft Azure engineers to our stable of certified security engineers. Together, we follow an Infrastructure as Code (IaC) and Configuration as Code (CaC) paradigm using software like Terraform to ensure consistency and uniformity to deployments. The graphic above includes the default selection of tools in use by our DevSecOps pipeline.
Realize enhanced security and other benefits
Our DevSecOps process is designed to deliver security, trusted code, and other benefits to your organization:
Secure by design: We integrate automated security guardrails and perform security reviews upon first code check-in. This allows for the fastest feedback on developed code with regards to security vulnerabilities. And, it prevents insecure code from making it to the development, staging, or production environments.
Cost reduction: With automated checks, our DevSecOps process finds security and code quality issues before the code even makes it out of the developer’s environment. This reduces development cost and engineer interventions, reduces the technical debt, and increases the return on investments (ROI).
Speed to ATO/production: An organization’s objective is to have much faster deployments and get Authority to Operate (ATO) certifications. By following established and agreed-upon security and review practices within DevSecOps, the developed code can reach the end-user in a far timelier manner.
Increased deployment/speed of operations: Automation is key to continuous deployment and to increasing the speed of the development lifecycle. Within our DevSecOps, automation allows for new environments to be created on-demand and in a consistently efficient manner.
Open-source library health/provenance: Our DevSecOps establishes a clear, legal view of open source software licenses and version updates (for example: are there restrictions on modification or redistribution?). Also, DevSecOps ensures that the latest security vulnerabilities research is properly surfaced to the correct stakeholders.
Measurability: With dashboards and quality gate checks, our DevSecOps prevents low-quality and insecure code from becoming part of the software code base at the earliest stages. Organizations get full traceability from the project management tool (Jira) and the code quality is measured by tools (SonarQube)—giving even more confidence in the deployed codebase.
Simplified governance: Automation helps greatly in simplified governance. Code reviews act as gate checks with required approvers. With our DevSecOps approach, code is only promoted when the approvals (which are tracked on every code review) are granted.
Getting started with DevSecOps
At every step of the DevSecOps, NT Concepts works with security in mind for our clients’ enterprises. Our processes empower organizations to be proactive in the software development lifecycle and help embrace continuous authority to operate (ATO).
With automated security checks, solutions are developed with the highest quality code, consistent deployments, and enhanced security.

As chief DevSecOps Engineer, CHRIS EDWARDS continuously improves our SDLC efficiency with open source tools, automation, security, and cloud resources to cut down on manual, time-consuming tasks so our developers and data scientists can concentrate on what they do best. His specialty is transforming our clients’ legacy systems with modern development approaches, platforms, and tools, integrating security every step of the way.